Wireless Network Analyzer's Overview - Part 4 (Guest Blog)
By Ernesto Fernandez On 09/16/2022
Wireless Network Analyzer Views and Features
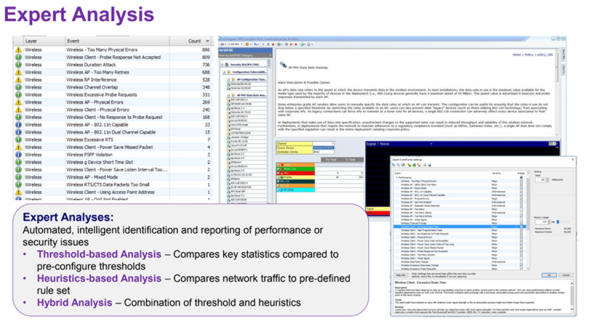
Expert Analysis
This feature is an automated, intelligent identification and reporting of performance or security issues. For this feature to work properly, you will have to create or set several baseline thresholds to be able to compare the newly received information, and this feature will also be able to notify you when one of the predefined measures is not met. There are three different baseline analyses you can set in some of the Wireless network Analyzers.
Threshold-base Analysis – Compare key statistics to pre-configure thresholds.
Heuristics-base Analysis – Compare network traffic to the pre-configure rule set.
Hybrid Analysis – Combination of threshold and heuristics.
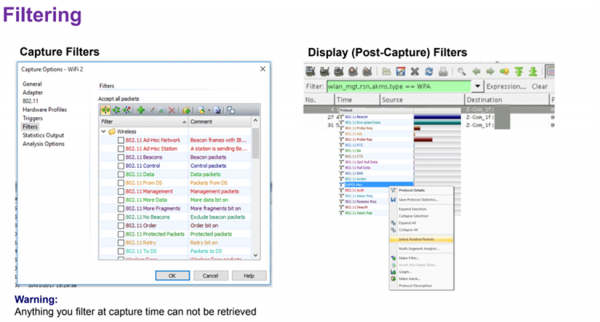
Filtering
There are two different types of filtering when doing wireless network analysis, and it is very important to understand the difference between the two. There are capture filters, and there are also display (post-capture) filters, they are described as follows.
Capture filters – with these filters, you will keep the frames that you want, and you will discard the frames that you don't want to keep at the time of the capturing. Very important to note the frames you discard with these filters will never be able to get retrieved again because they were never captured during this analysis.
Display (post-capture) filters – with these filters, you will be able to filter what is on the display view or what you are seeing. You would be able to display filter a capture file that was also filtered during the capture.
It is recommended to filter the capture files with the display filter and not with the capture filters unless absolutely necessary or you are certain of the traffic you are looking for during this particular analysis.
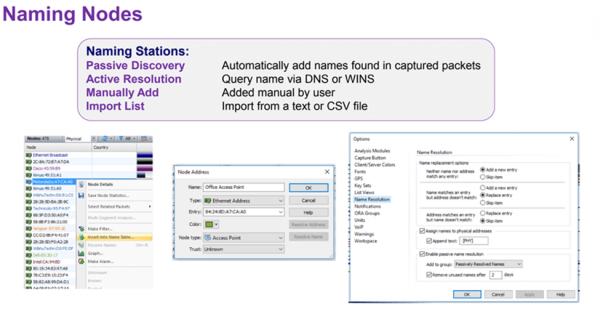
Naming Nodes
This feature will allow you to view the names of the devices instead of the MAC addresses, which would help you identify devices easier and be able to follow the device during different processes of wireless communication. There are different ways you can name the devices when using this feature and they are described below.
Passive Discovery – Automatically will add the names found in the packet captures, however, for this method to work, you will have to have access to the upper layers.
Active Resolution – This method will query the names of devices via DNS or WINS, however, for this method to work, you will have to have access to the upper layers.
Manually adding – In this method, you will need to manually add the name of the devices into the Wireless network Analyzer.
Import List of devices – This method will allow you to import a list of mapping device names to MAC addresses via a text or CSV file.
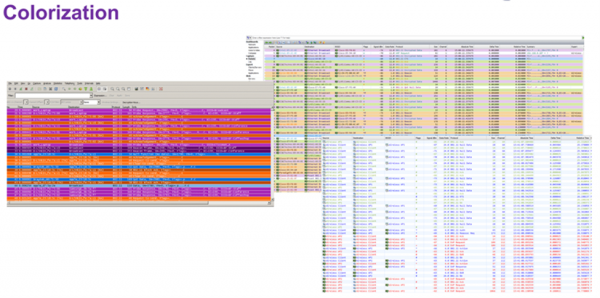
Colorization
With this feature, you will be able to separate protocols/frames by color. This feature will also help you, instead of filtering the display, with visually identifying what you are looking for quicker. This feature could be set up however you would like, and it could also be saved to be used with other analyses, or you can also have multiple different colorization schemes to be used for different types of traffic captures. There are several websites offering different coloring rules.
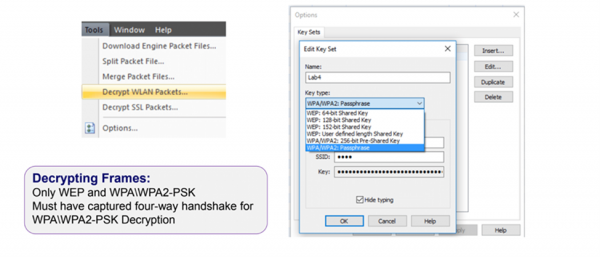
Decrypting Frames for upper layer visibility
This feature offers you the ability to decrypt the frames captured during the analysis. However, there are a few conditions that will need to be met to decrypt the data payload on the frame.
The encryption used – This feature can only decrypt frames using WEP and frames using WPA/WPA2-PSK. This feature will not be able to decrypt frames using 802.1X EAP.
Four-way handshake – You will also need to have captured the four-way handshake along with the SSID and the passphrase to be able to decrypt the frames.
It is recommended that if you need to decrypt those frames, you will have to force the device to disconnect and reconnect to capture the four-way handshake with SSID and Pre-
Shared key then be able to decrypt the traffic.
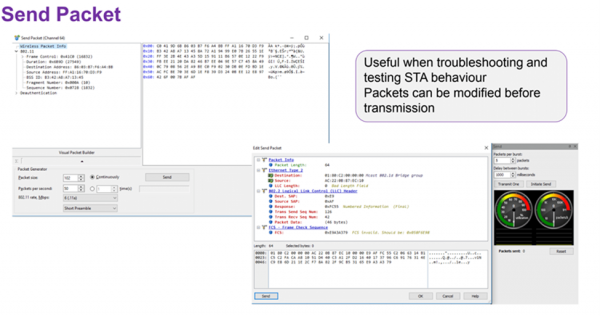
Packet Generation
This feature allows you to generate a packet to send to either an access point or to a device on the wireless network environment. These generated packets can be modified before transmission. This feature is not available in all Wireless network Analyzers and can be used for troubleshooting and/or testing a device or access point behavior when a generated packet is received.
Conclusion
In conclusion, this series of articles has been intended to give you an idea or perspective of the different views, features, capabilities, and opportunities a Wireless network Analyzer can provide you with assistance in your daily lives as a Wireless network professional. I encourage you to decide, which Wireless network Analyzer works best for you based on budget, features, capabilities, and learn as much as possible about it by either searching online for material or by utilizing the software as much as possible.
To read this series from the start, click here.
Reference table:
Material by – CWAP (Certified Wireless Analysis Professional) Study and reference guide, CWAP-403 1st edition by Certitrek publications.
Illustrations by – Wireless Analysis and Troubleshooting CWAP bootcamp v1.1, MarQuest networking support by Peter Mackenzie.
Blog Disclaimer: The opinions expressed within these blog posts are solely the author’s and do not reflect the opinions and beliefs of the Certitrek, CWNP or its affiliates.



