Review of Nokia N800 for Wireless LANs
By CWNP On 08/07/2007 - 12 Comments
Earlier this year Nokia released an updated version of their popular Nokia N770 Internet Tablet. The N800 excels at being a small, light-weight device capable of WiFi as well as Bluetooth access to the Internet. THis is a user-based review of this great little device.
Review of Nokia N800 for Wireless LANs
Earlier this year Nokia released an updated version of their popular Nokia N770 Internet Tablet. The N800 excels at being a small, light-weight device capable of WiFi as well as Bluetooth access to the Internet.
I could go on an on about how this little device has changed how we access the Internet in our home. Instead of lugging around laptops, we have a couple of N800s that the kids access for Internet queries, (just what High School did ‘King James’ go to – while watching the playoffs), to googling, to streaming music, conducting mulit-user IM sessions, to just about anything you’d want to use the Internet for – but in a very small package.
The screen resolution is amazing! If the iPhone has this screen, I’ll be in line to buy one. Even though I’m so old now I have to use bi-focals to read the small stuff – I’m comfortable with the N800’s little screen – the resolution makes it possible to fit so much in a little package.
But for the interest of this Blog I’ll move on to the use of the N800 in a wireless analysis mode.
I saw an announcement for a new piece of wireless security gear – called a Silica. This software/hardware bundle puts the intelligent penetration attacks and exploits of Immunity’s Canvas software in a small Nokia. It looked WAY COOL and I *wanted* to have one. But the $3,600 cost felt a bit prohibitive.
I’ve since had a chance to play with a Silica – and was suitably impressed – I still haven’t parted with the $3,600 but here’s a bit of a review of the tool.
This is a customized version of the Canvas tool – shoehorned into this small form-factor Linux device (Nokia N800) It is VERY easy to use. Just turn it on and click the start scan…
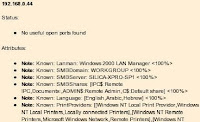
It will run through a series of scans of the local wireless networks, then attempt to penetrate using a variety of currently known exploits to find and exploit holes in your wireless LAN. It’s like having a little team of hackers sitting in you hand.
I’ve found it to be easy to run with the Nokia in your pocket. Very unobtrusive! – but in reality it takes up to 20-25 minutes to do a full attack against a single AP. Not like while doing a real penetration test you’ll have an excuse to ‘hang around’ a specific area waiting for the attack to finish. (Though you could easily hide the device and come back to pick it up later – but that $3,600 cost will probably make you think twice about leaving it outside of your view)
The reports it gives are in HTML format – you can just e-mail them to yourself, or copy them off onto the SD cards used by the N800
It does a pretty cool thing when attacking a MAC-Filtered AP – it automatically finds an associated STA and spoofs it MAC address to get associated.
It doesn’t do ANY WEP Cracking or WPA cracking, or anything but the exploits that are in Canvas.
Ok, now for the less expensive, yet still fun stuff using a Nokia N800. As part of our Wireless LAN Security Assessment Toolkit course development. We came across the N800s, fell in love with them, then re-arranged and re-wrote many of our course lab exercises to specifically use the N800s. We added wVoIP, video over IP, as well as catching IM traffic, web browsing, and other conversations sent over wireless to use the N800 as our client of choice when ‘watching’ the open Wireless LANs and re-constructing conversations via packet capture.
Then we thought, “is there anything more we can use the N800s for?”
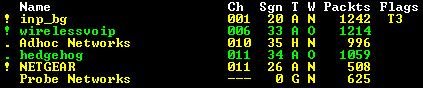
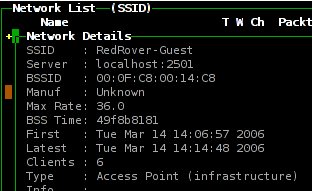
Since the N800 is just a little Linux computer… we added SSH, Terminal Shell, VNC, FTP, etc. to the system. Then once we got that running, it was a quick couple of steps to get Kismet and Metasploit running!
So just using Open Source software we were able to take the little $400 Nokia N800 and make it ‘like’ a Silica!

Just slip this little ‘bad boy’ in your pocket running kismet and go WarWalking to get all the APs in your area, including finding ‘hidden’ SSIDs. Or, start Metasploit and let ‘r rip – attempting whatever known exploits are available for Metasploit.
(By the way – this is NOT a fast device for Metasploit – but Way Cool to have running)
On the other hand – it makes a great Kismet platform!
We’ve got ours running the classroom with GoogleTalk and Gizmo Project for wVoIP and IM – but you have to have a Wifi access to use it, so this wont’ take the place of your cell phone. (It is possible to pair this device via Bluetooth to a cell phone running G3 speeds – but the easy way is with Wifi)
One more thing that is just *fun* to use the Nokia N800 and Wireless LANs – and I found this out by accident. I was testing in our offices a new access point – so I had the N800 associate to this new AP and started a ‘Hitcast’ session listening to some Internet Radio station. I kind of liked the station and so put the ‘radio’ in my pocket so I could have some tunes with me as I finished up writing up the analysis of this new AP. I checked my watch and realized the mail would have arrived, so I went out to the mailbox – down a long flight of stairs, outside the steel-sided building my office is in, and across the parking lot to the community mailbox to check the mail.
It wasn’t until I was heading back up the stairs and a co-worker commented on my choice of music that I noticed this little wonder continued to stream music the entire way. Thus was born the Audio Site Survey! Just associate, then walk till the music drops… Simple easy and leaves your hands free to work on other things while doing a fairly decent site survey. Cool!
Enjoy!
Keith Parsons - Managing Director
Institute for Network Professionals/HOT Labs
Blog Disclaimer: The opinions expressed within these blog posts are solely the author’s and do not reflect the opinions and beliefs of the Certitrek, CWNP or its affiliates.








0 Responses to Review of Nokia N800 for Wireless LANs
Subscribe by EmailThere are no comments yet.
<< prev - comments page 1 of 1 - next >>
Leave a Reply
Please login or sign-up to add your comment.